Streamlining Digital Forensics Investigations with Cyber Triage
In this blog, we delve into the practical application of Cyber Triage tools in analyzing a host compromised by the infamous WannaCry ransomware. Cyber Triage, a powerful incident response tool, simplifies the process of collecting, analyzing, and correlating digital evidence to identify the root cause and impact of an attack.
By leveraging its advanced capabilities, investigators can streamline forensic workflows and enhance the efficiency of their investigations. Visit Cyber Triage’s official page to learn more or evaluate the tool. This blog provides actionable insights into how Cyber Triage can be a game-changer in forensic investigations, making it a valuable resource for DFIR professionals and cybersecurity enthusiasts.
View of compromised host that has been acquired
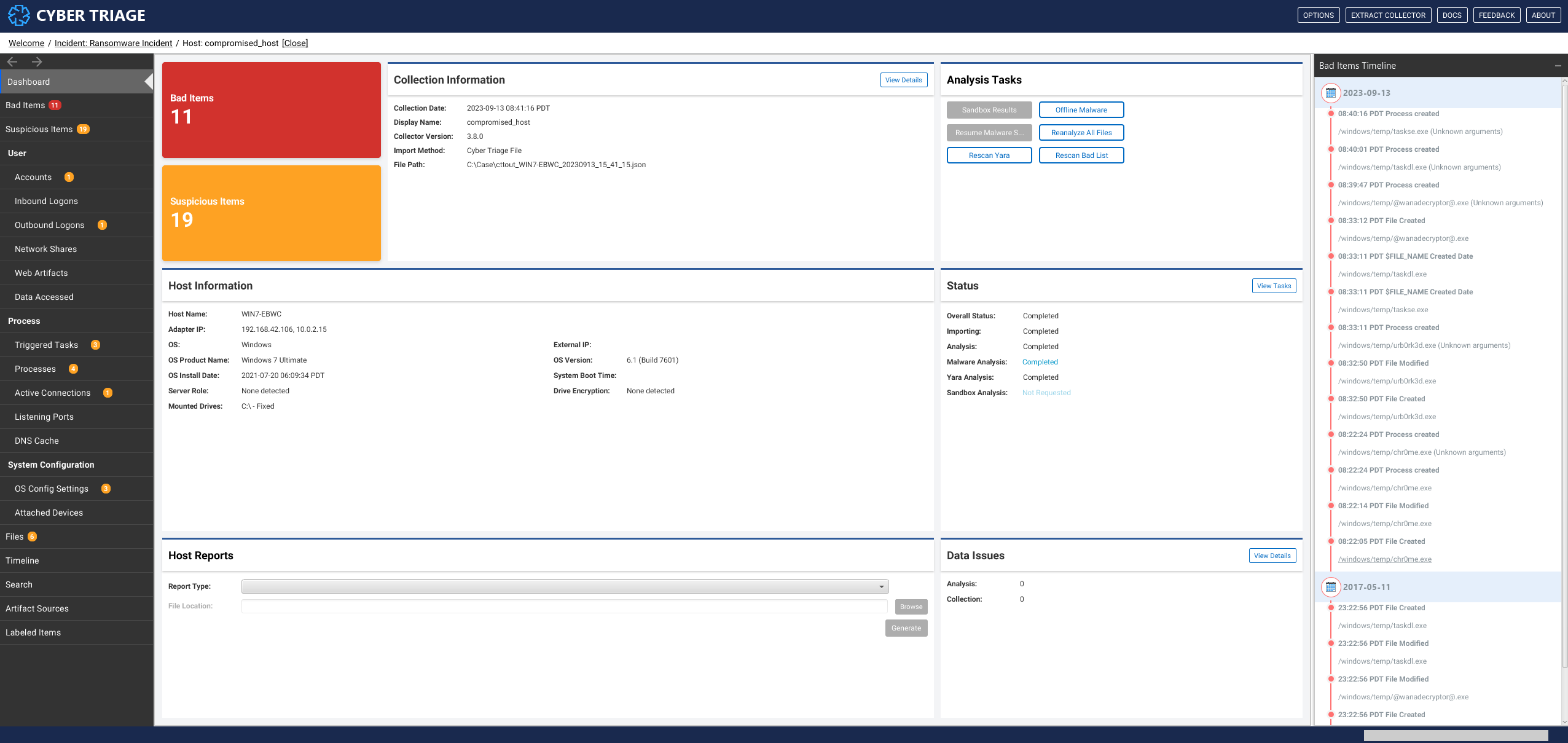
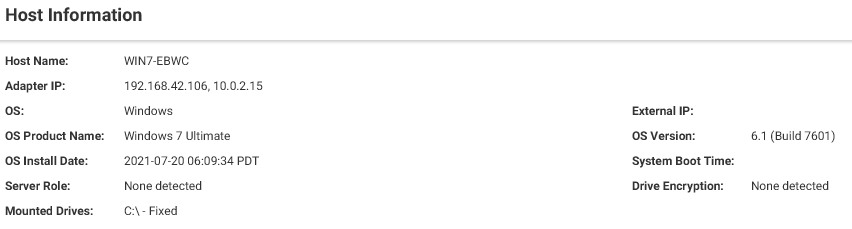
Basic Host Information
Host compromised was built with Windows 7 Ultimate - version 6.1 (Build 7601)
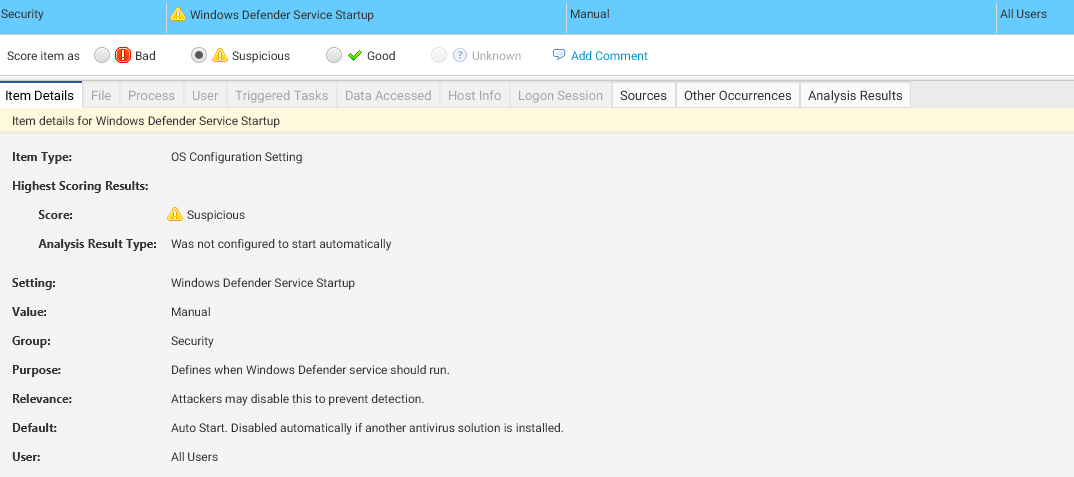
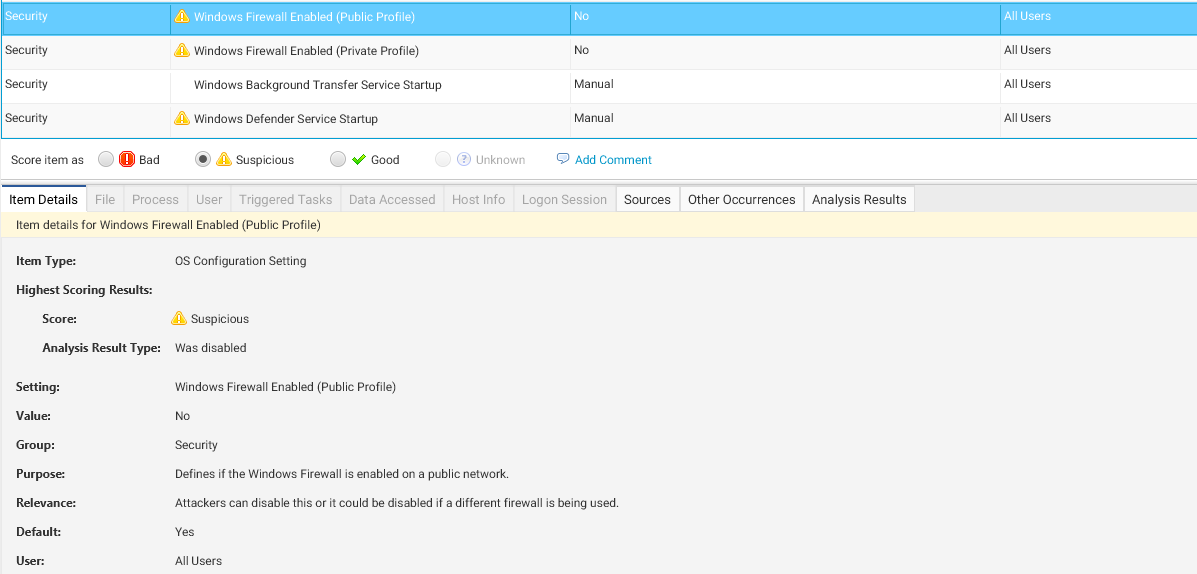
We can see that Windows Defender Startup is set to Manual & Firewall is not enabled and indicated with score Suspicious
Initial Access
This image shows how Cyber Triage helps identify the point of entry used by WannaCry. The presence of suspicious connections or exploit attempts, like the EternalBlue vulnerability, is highlighted here.
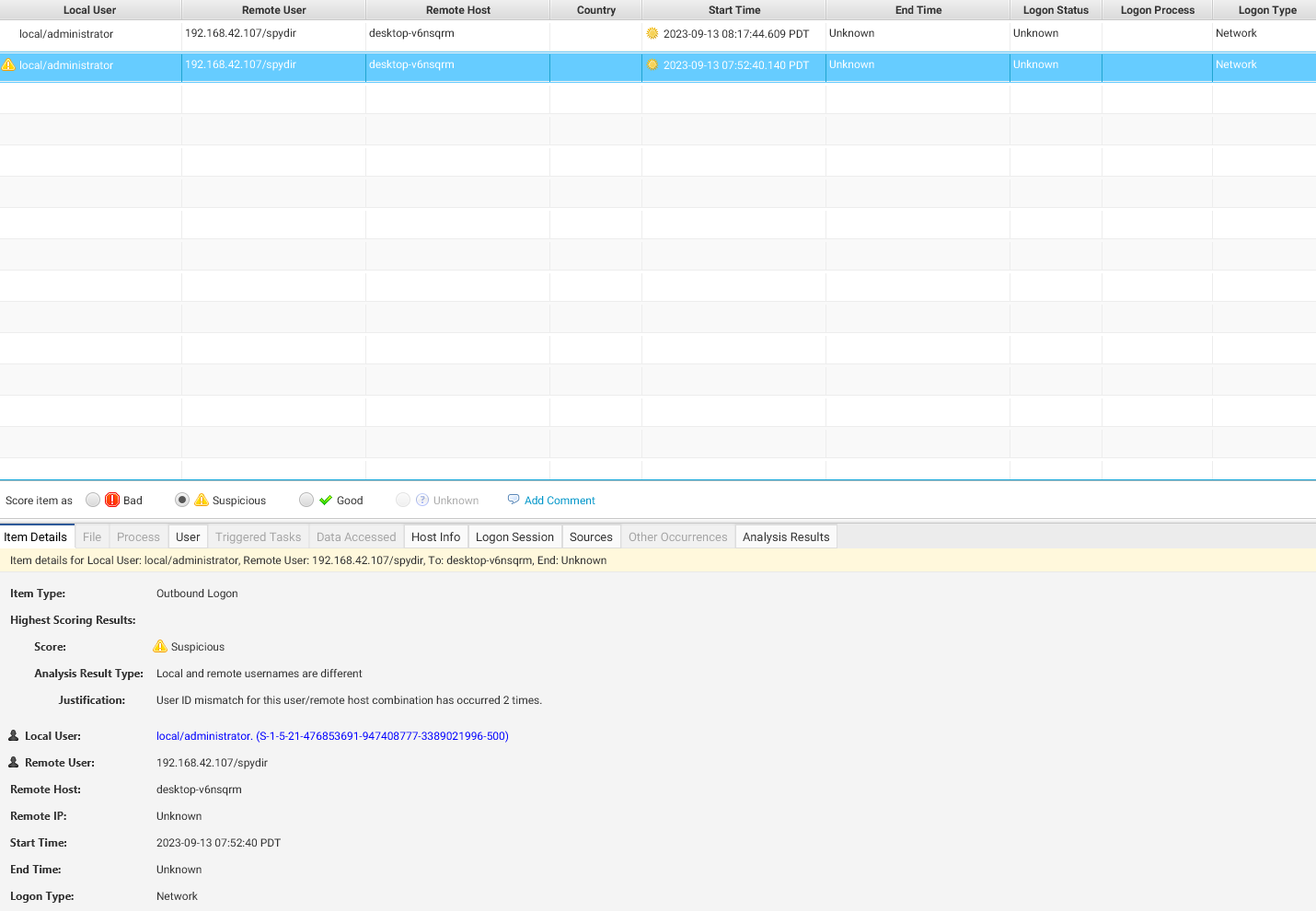
With EternalBlue vulnerability threat actor exploit the system and sent some suspicious binary
We can see the timeline threat actor get in to system
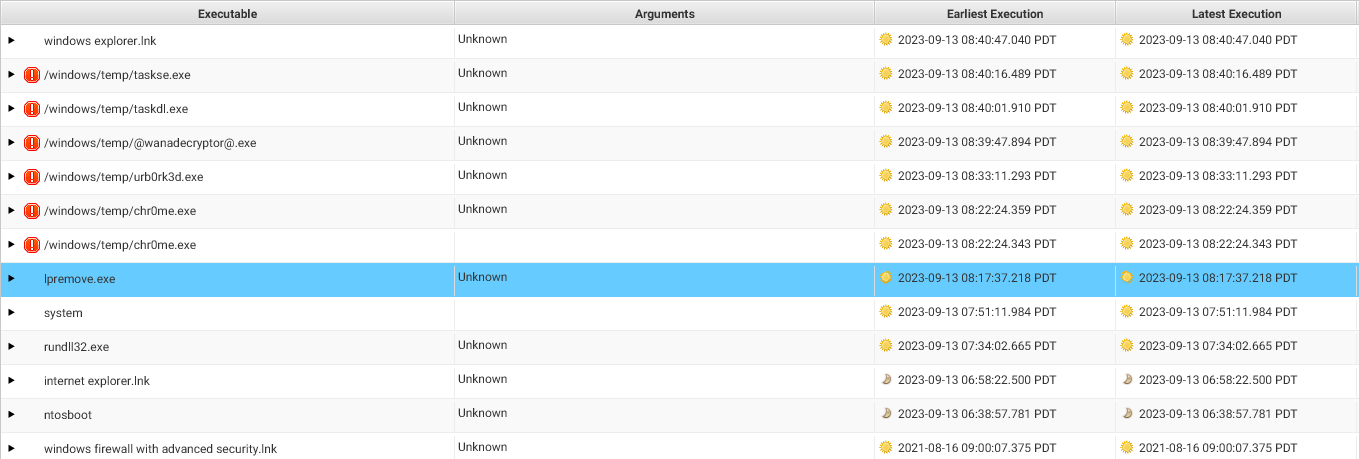
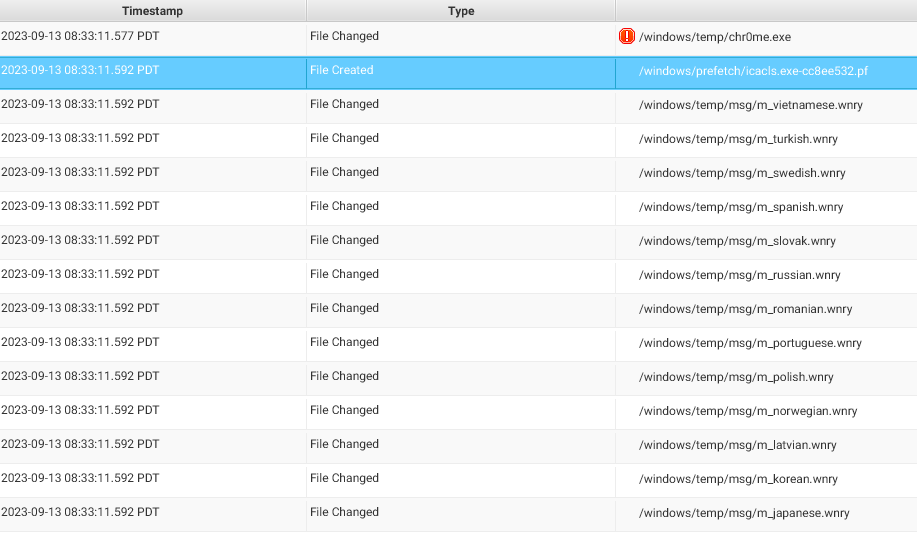
Execution
They created startup item/shedule task for their malicious activity on path /Windows/temp/tasksche.exe
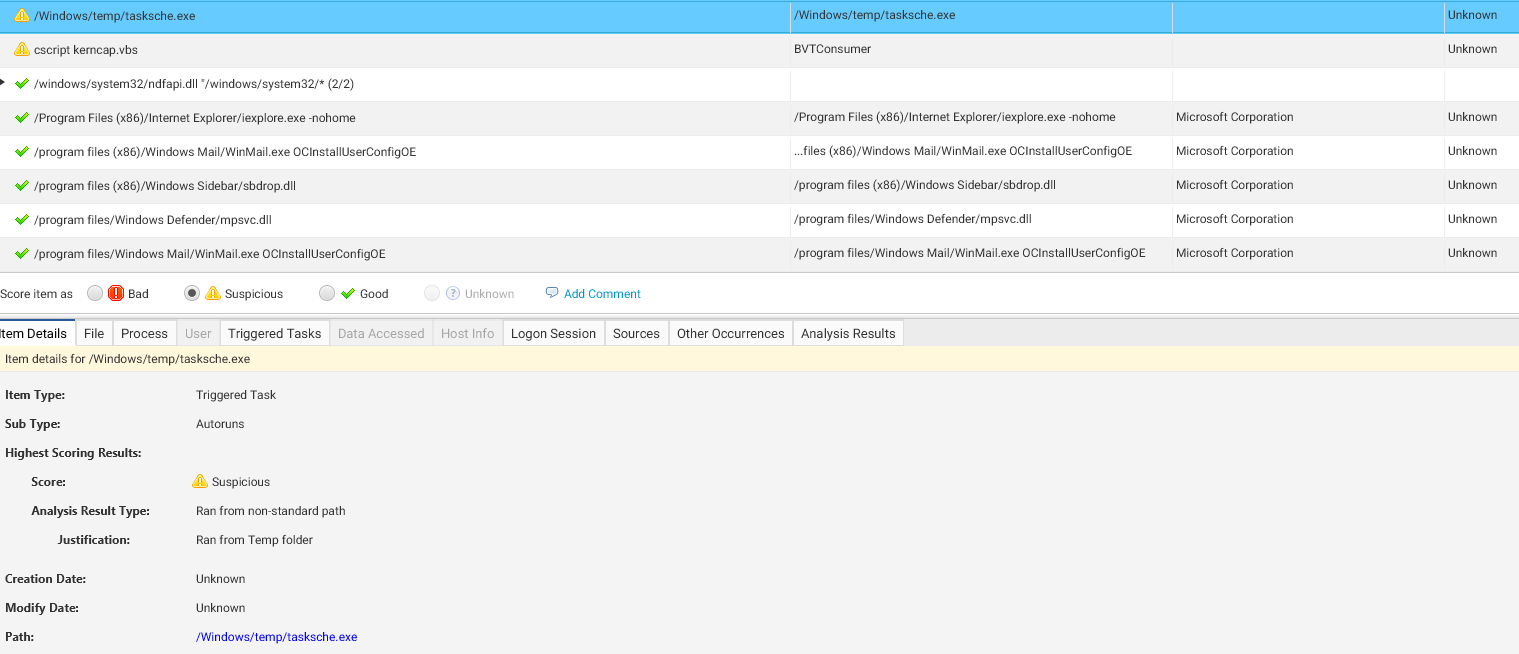
Threat actor stored their tools on directory C:\Windows\Temp this commonly used by threat actor because globally writeable. They used Sliver C2 as a command control
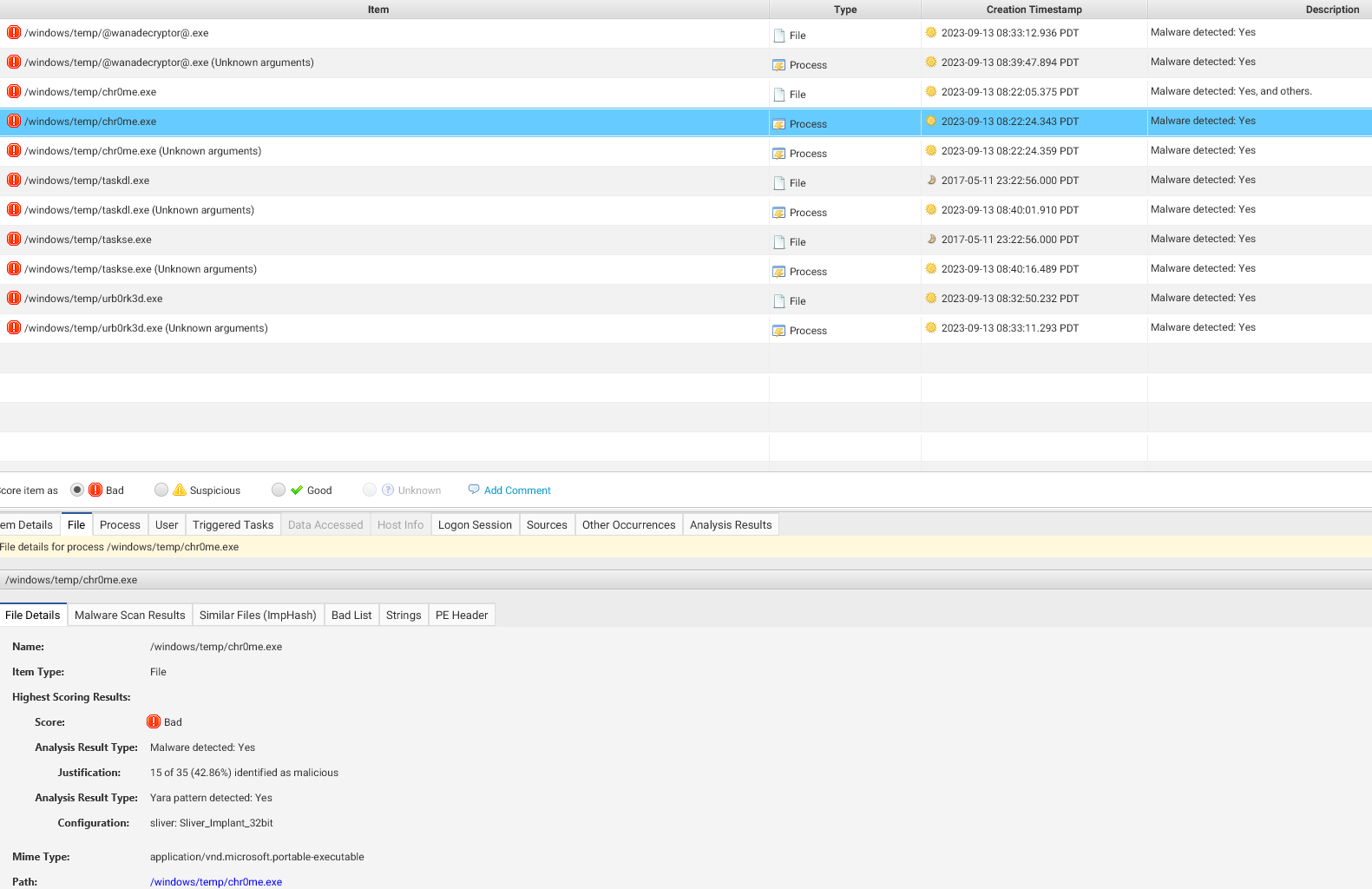
This image shows processes associated with the ransomware. Cyber Triage identifies abnormal file and process behavior, helping investigators trace the execution phase of WannaCry
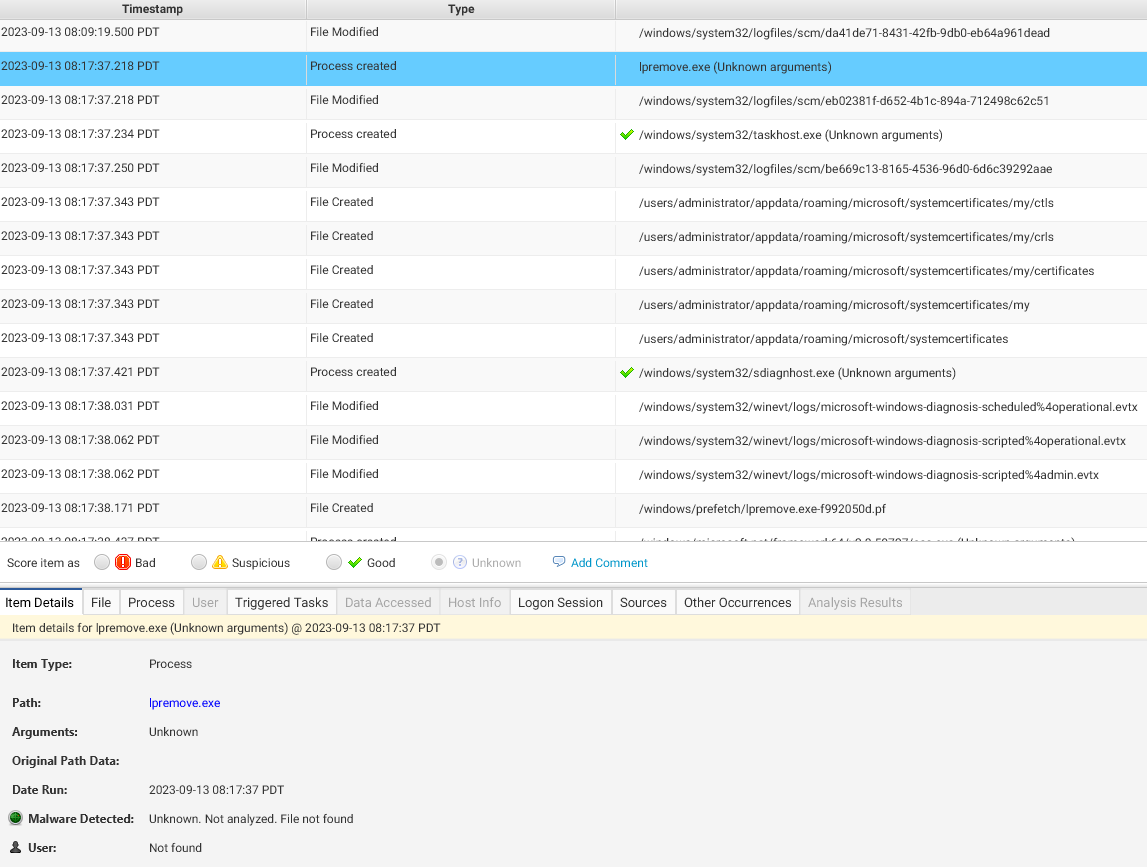
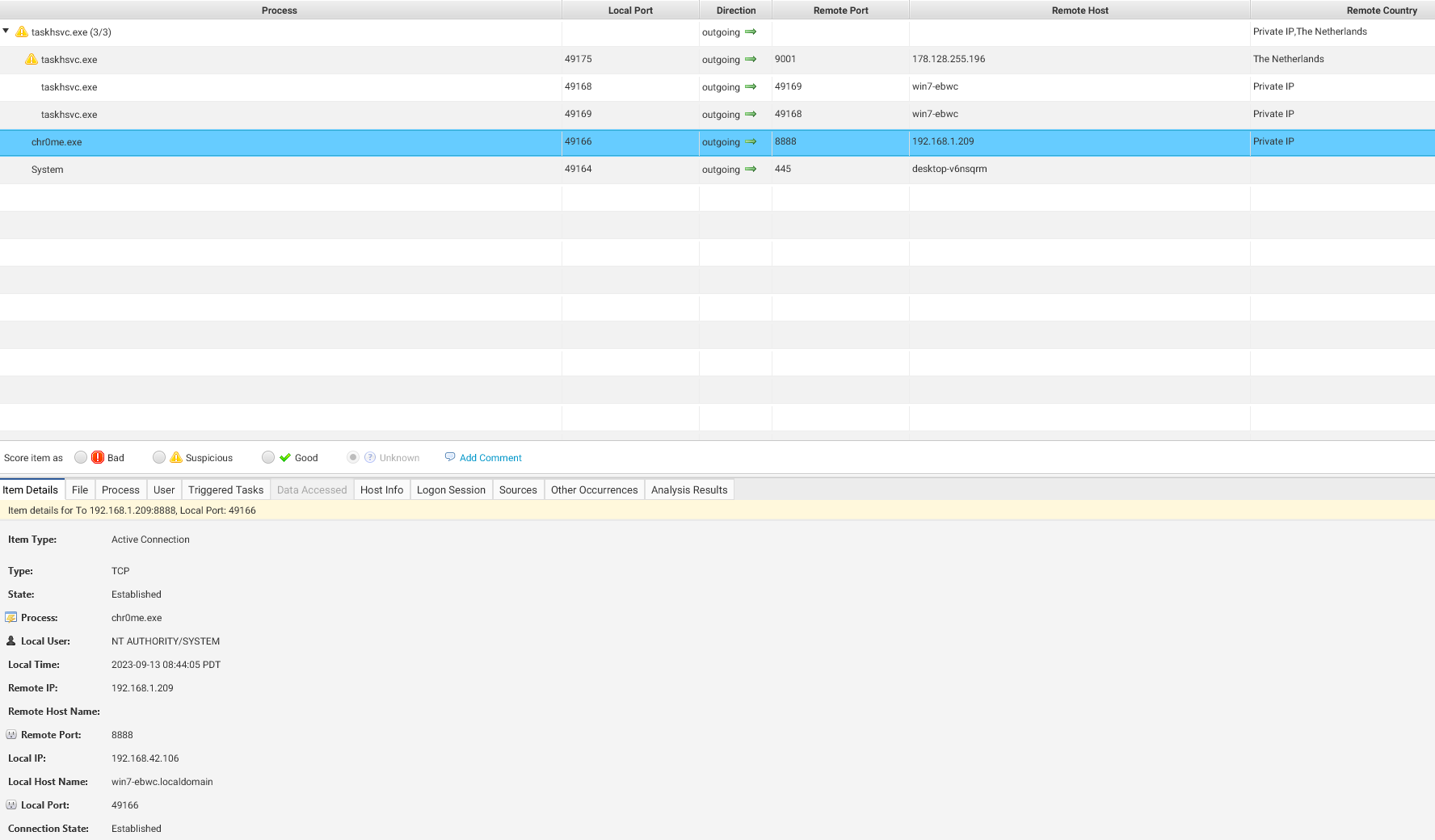
Command & Control
Timeline for threat actor created C2 malware on victim host and with filename and path 11:22:05am EDT September 14
/windows/temp/chr0me.exe
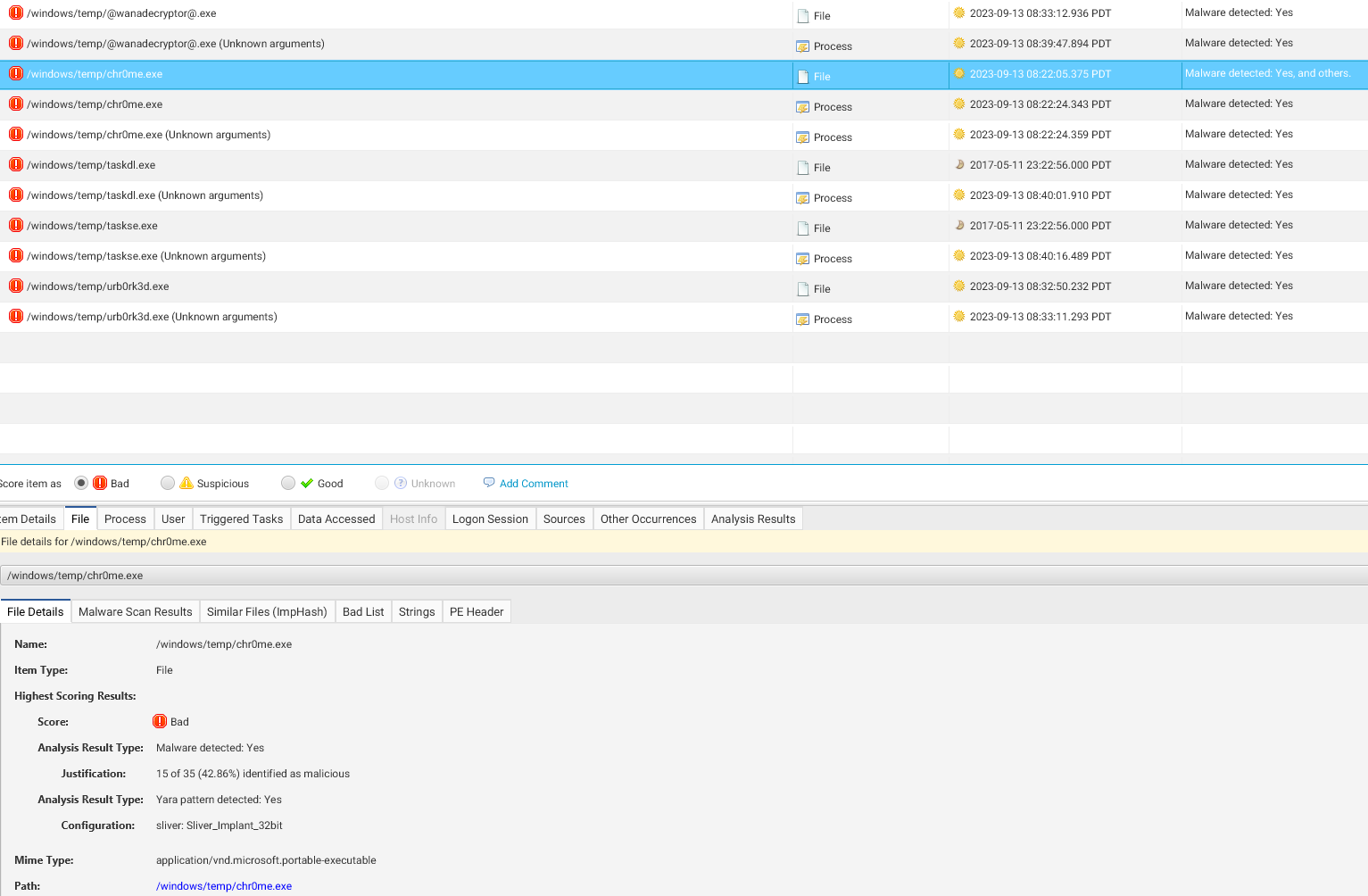
192.168.1.209 is the call-back IP address for the C2 malware.
Here, Cyber Triage helps detect communication between the compromised host and the attacker’s C2 server. Anomalous outbound network traffic or suspicious DNS requests often indicate C2 activity.
Impact
/windows/temp/urb0rk3d.exe
This image illustrates the encrypted files on the host. Cyber Triage helps investigators quickly recognize the encrypted data, assisting in the assessment of the attack’s full impact.
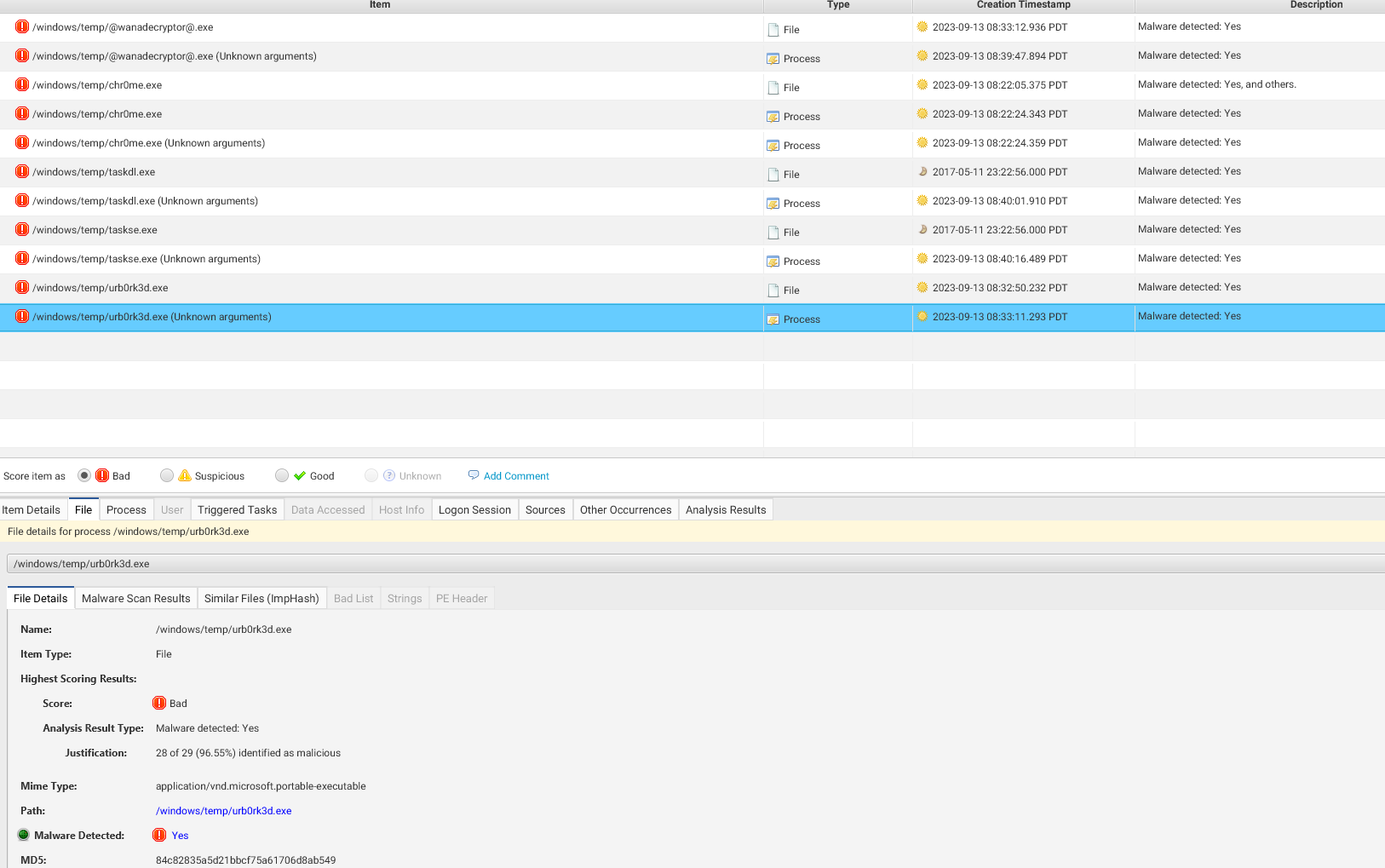
Once deployed, WannaCry encrypted crucial files, making them inaccessible to the user. It’s important to note how Cyber Triage helped investigators quickly identify the malware’s presence and scope.
WannaCry ransomware incident emphasizes the importance of using advanced tools like Cyber Triage in cybersecurity investigations. Key takeaways include the need for regular patching to close vulnerabilities such as MS17-010, the effectiveness of Cyber Triage in speeding up the response and recovery process. For organizations aiming to improve their cybersecurity posture, adopting proactive threat detection and response strategies like these is critical in defending against future threats.
Indicators of Compromise
| IP address |
|---|
| 128[.]31[.]0[.]39 |
| 149[.]202[.]160[.]69 |
| 46[.]101[.]166[.]19 |
| 91[.]121[.]65[.]179 |
| Domains |
|---|
| hxxp://www[.]btcfrog[.]com/qr/bitcoinpng[.]php?address |
| hxxp://www[.]rentasyventas[.]com/incluir/rk/imagenes[.]html |
| hxxp://www[.]rentasyventas[.]com/incluir/rk/imagenes[.]html?retencion=081525418 |
| hxxp://gx7ekbenv2riucmf[.]onion |
| Hashes |
|---|
| 5a89aac6c8259abbba2fa2ad3fcefc6e |
| 05da32043b1e3a147de634c550f1954d |
| 8e97637474ab77441ae5add3f3325753 |
| c9ede1054fef33720f9fa97f5e8abe49 |
